[Written in partnership with Microsoft Malaysia, but the editorial team had full control over the content.]
“Data is one of your crown jewels.”
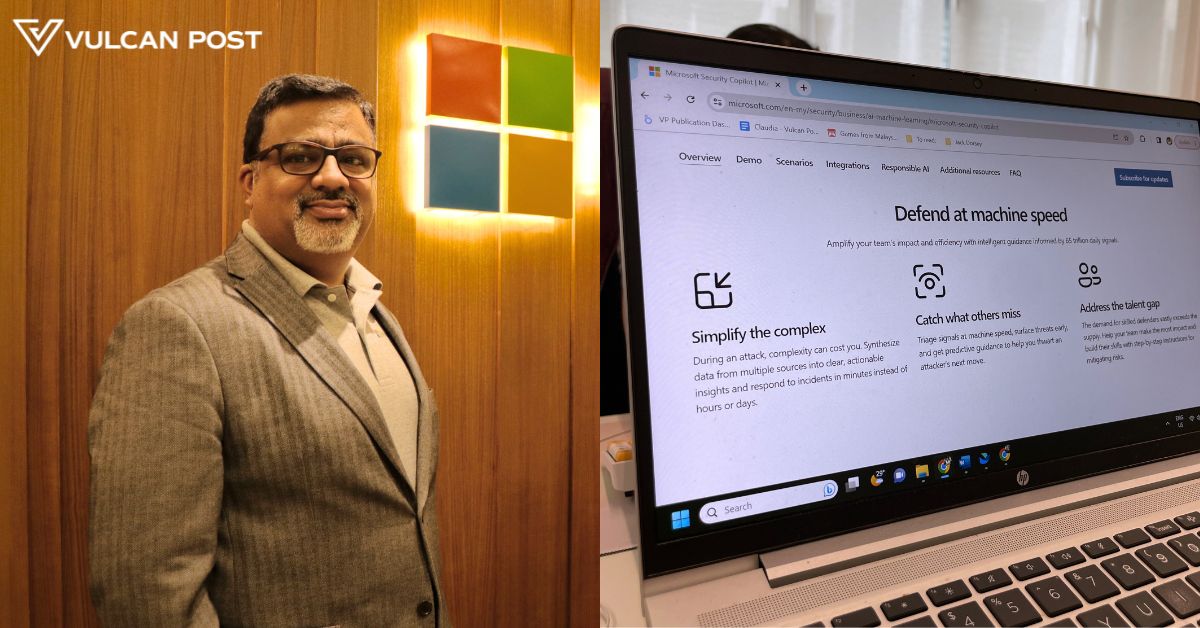
This is something that Abbas Kudrati, Microsoft’s APAC chief cybersecurity advisor, emphasised during an interview with Vulcan Post.
In today’s world, almost everyone is leaving behind some kind of digital footprint. With that comes an abundance of data, some of which are stored on your phone, on online platforms, or on the cloud.
And this data may be vulnerable.
“Hackers want to sell your data,” Abbas said. “It could be juicy information that you have, it could be customer information, it could be employee information.”

Over the years, cyber threats have become very advanced. For one, using social engineering attacks, hackers may exploit human behaviours and emotions to get what they want.
An example of this is by phishing—sending emails impersonating reputable institutions such as banks, the police, or even Microsoft itself.
“Hackers don’t differentiate whether you are a small company with five employees or 50,000 employees. For them, you are just one target.”
Thus, here are some lessons entrepreneurs of SMEs and beyond should keep in mind to ensure they are as resilient to cyber attacks as possible.
1. Have an assume breach mindset
As its name suggests, an assume breach mindset involves a more pessimistic approach whereby you assume cyber attacks will happen instead of assuming they might happen.
This shift in mindset makes for a more active defense system rather than a passive one. A result of having such a mindset typically involves layers of controls.
This is so that if the first control fails, the second control will be enabled. Essentially, you assume that someone can and will overcome the first wall of protection.
This mindset is the basis for many of the tips to come.
2. Create a human firewall
This means that employers need to educate their own staff members and ensure they are aware of how attackers may take advantage of human emotions.
This can be done so through security awareness programmes and other kinds of training.
3. Implement multi-factor authentication
While multifactor authentication has already become common practice for many, it never hurts to reiterate it again.
Of course, having a strong, alphanumeric password is the first step. But going one step beyond and implementing multi-factor authentication can better ensure identities, usernames, and passwords are secure.
Abbas mentioned three options of authentication: something you have (token or an authenticator app), something you know (password or a pin), and something you are (biometrics).
By applying two out of three of these options, you can establish a multi-factor authentication system.
“By using that, you will not be compromised, because the second-factor authentication is with you and not with the hackers or adversaries,” Abbas said.
4. Catch, match, patch
Another three-step system SMEs can keep in mind to protect themselves is something Abbas calls “catch, match, and patch”.
The catch portion involves finding the bad behaviour or identifying the adversaries. This can be done using good antivirus or antimalware solution, such as Microsoft Defender for Endpoint.
Matching is about assigning the right person to have access to the right data. That means you shouldn’t open up full rights or full access to everyone in the company.
“Make sure you have given access based on role, or need-to-know, need-to-do basis kind of principle,” Abbas advised.
Finally, all the systems in your patching environment must be up to date so hackers cannot exploit vulnerabilities.
5. Backup your information
While prevention is better than cure, it’s important to keep the assume breach mindset and prepare for scenarios whereby the hacker does make it past your security.
This involves preparing backups of critical information. This is so that if hackers ask for money, you have the leverage of saying no, as you can recover data from your backups.
You should also take note of resources and contacts you can reach out to should you undergo a cyber attack.
In Malaysia, there are also government organisations that can provide help, especially for SMEs. Abbas highlighted MyCERT (Malaysia Computer Emergency Response Team) as a useful resource.
Of course, businesses that can afford it can also engage with cyber-security specialists and agencies.
6. Ensure you can easily monitor your cyber security
“Because of the number of threats we are getting today, we have to act at the speed of an attack,” Abbas said.
To do this, you need a robust monitoring system that can identify threats and deal with attacks immediately.
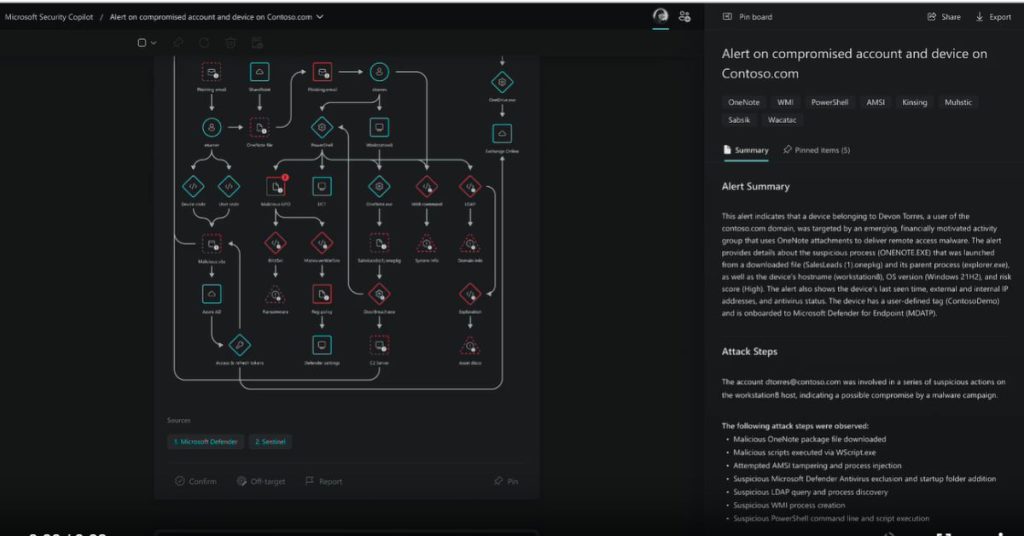
Microsoft Security Copilot is one such solution.
Launched earlier this year, Microsoft Security Copilot is a security analysis tool that is powered by AI so that analysts can quickly respond to threats and effectively process signals at machine speed. This helps assess risk exposure in mere minutes.
The innovation is based on generative AI and large language models, Abbas shared.
Similar to how ChatGPT and other AI-powered chatbots function, Microsoft Security Copilot has a prompt bar where any user can type in simple questions and receive assistance from the programme.
This tool helps by consolidating all the necessary cyber security information into one accessible window, which also helps to reduce inspection time. The ease with which it can be used also means that it requires a smaller workforce for one task.
Microsoft Security Copilot is still in preview, though, and not available to the general public just yet. Those interested in announcements can sign up for updates from Microsoft.
100% cybersecurity is a myth
The idea of a completely failproof system might be daunting. On top of that, it’s also a myth. While you can never guarantee you’ll never be hacked, what you can do is be more cyber resilient.
Hence, it’s important to keep all these tips in mind even though you might not be facing any threats right now.
As Abbas said, “You may get hit today or tomorrow from cyber attacks, but how quickly you can recover out of that attack is what cyber resilience is all about.”
For more about what cyber resilience is all about, watch our reel with Abbas here:
And watch Abbas talk more about how SMEs can protect themselves against cyber attacks here:
- Learn more about Microsoft Security Copilot here.
- Read other articles we’ve written about Microsoft here.